Live Status Privacy Policy
Your trust is our responsibility. This Live Status system is built with enterprise-grade security, transparent data handling, and real-time protection mechanisms.
Data Protection
All live-status data is encrypted end-to-end using modern TLS standards. We never expose user metadata publicly.
Secure Infrastructure
Our infrastructure is protected by multi-layer firewalls and continuous monitoring systems.
Transparent Visibility
Users can see exactly what data is collected and how it is used through our clear dashboard policies.
Minimal Data Collection
We only collect necessary live-status signals required to maintain performance and reliability.
Global Compliance
Our privacy framework aligns with international data standards and regional compliance laws.
Real-Time Alerts
Users are instantly notified about any system changes impacting their live visibility.
Built For Secure Real-Time Monitoring
Our Live Status system ensures privacy-first tracking while maintaining transparency and system performance. Every signal is anonymized, every request validated, and every update securely processed. We believe in elegant engineering combined with responsible data architecture.
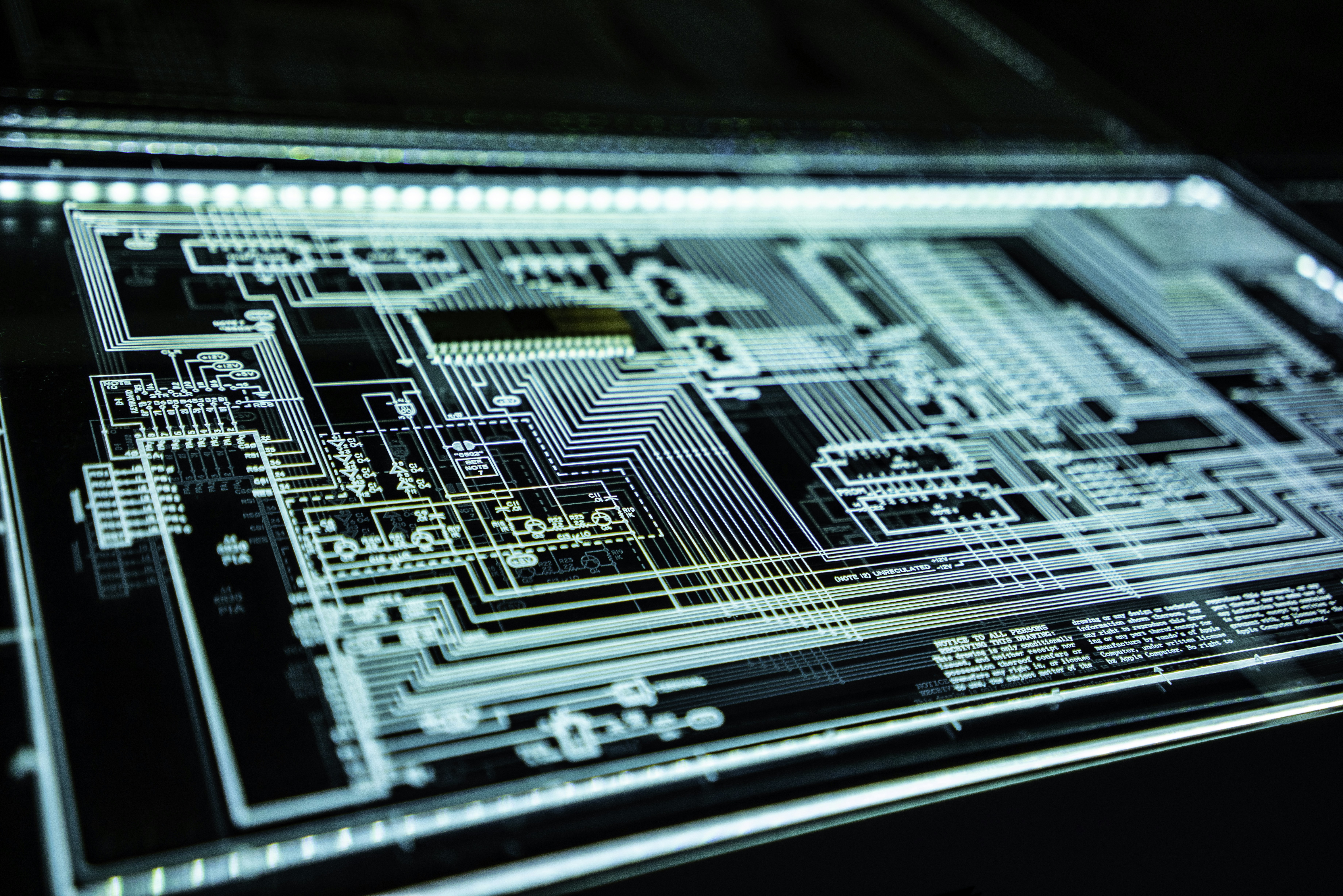
Privacy Designed With Modern Standards
Our Live Status infrastructure is architected with a privacy-first mindset. We implement multi-layer encryption protocols, real-time anomaly detection, zero-trust authentication systems, and global compliance standards to ensure that user data remains protected at every interaction point. Every request is verified, every signal encrypted, and every access point intelligently monitored. Privacy is not just a feature — it is our core engineering philosophy.

Zero-Trust Architecture
Every connection is authenticated and continuously validated. No implicit trust, no unsecured access.
End-to-End Encryption
All live signals are encrypted during transit and storage using modern cryptographic standards.
Global Compliance
Aligned with international data regulations and region-specific compliance frameworks.
Real-Time Threat Detection
Advanced monitoring systems detect anomalies instantly to prevent breaches before impact.
Modern privacy demands more than policy statements — it requires intelligent system design. Our Live Status framework uses isolated data containers, adaptive encryption keys, and automated policy enforcement engines to ensure that sensitive metadata never becomes vulnerable. Access logs are immutable, system audits are automated, and transparency dashboards give users full clarity into how their data flows through the ecosystem. We engineer privacy the same way we engineer performance — precisely, elegantly, and without compromise.